
The BuilderStorm application runs on OVH – providing a high level of reliability and security.
Linux – Nginx – PHP – MySQL
Note: these are subject to change
Every system no matter how well maintained is susceptible to some form of failure. However, with the procedures we have in place, it is unlikely we will suffer any data loss. The short-term and long-term backups ensure that we cater for events such as physical hard-drive failures or data becoming corrupted and going unnoticed, however unlikely.
Note: These are both highly unlikely events and are used as examples.
Manual Backups – we have the facility to take manual backups if required, which can be made on request.
We have the facility to export certain data from BuilderStorm and place this within your own One Drive account. This ensures that you always have access to the data, regardless of the availability of our own services.
Note: This will need to be pre-arranged with details on what data is to be exported.
Your data is extremely sensitive and for that reason it’s stored in an encrypted state at all times.
We run additional software on top of other server packages to manage our web server as well as our authentication, web server security, antispam, antivirus and network security. It adds another layer of protection along with its monitoring scripts providing server health reports and other warnings/reports. Security & DNS.
Managed through CloudFlare – https://www.cloudflare.com/
Our web traffic is routed through CloudFlare’s intelligent global network. They automatically optimise the delivery of our application. They also block threats and limit abusive bots and crawlers from wasting bandwidth and server resources. The result: a significant improvement in performance and a decrease in spam and other attacks.
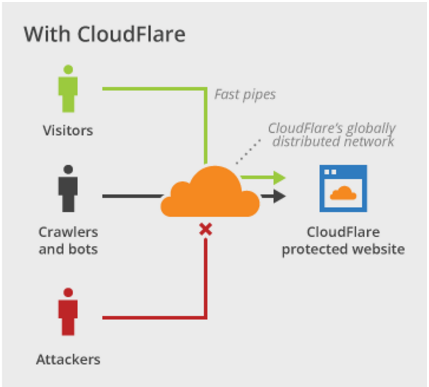
CloudFlare’s technology automatically detects new attacks that arise against any website on its network. Once CloudFlare identifies a new attack, it starts to block the attack, both for the particular website and the entire community.
We ensure that your communication is encrypted at all times through Secure Socket Layer.
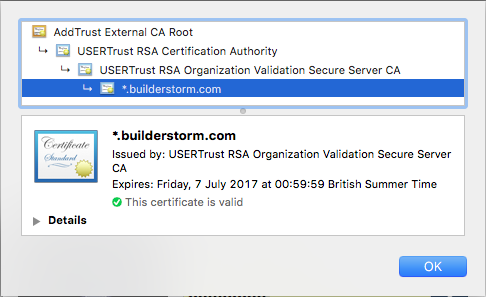
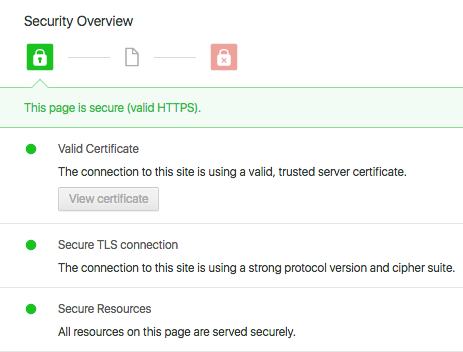
Our service runs through CloudFlare’s ‘Full SSL (strict)’ mode: encrypts the connection between your computer and CloudFlare, and from CloudFlare to our server. Our SSL certificate is signed by a trusted certificate authority. You will always see the SSL lock icon in your browser.
CloudFlare has built-in security to protect against DDoS and other attacks. Built from the ground up with security in mind, their DNS service can resist the largest DDoS attacks. Based on their experience with handling attacks, and their custom authoritative DNS software, CloudFlare automatically applies the proper protections, including rate limiting, filtering, and blocking.
We run software that manages traffic to our site. It scans log files and bans IPs that show malicious signs – too many password failures, seeking for exploits, etc. This is used to update our firewall rules to reject the IP addresses for a specified amount of time.
We run software that manages traffic to our site. It scans log files and bans IPs that show malicious signs – too many password failures, seeking for exploits, etc. This is used to update our firewall rules to reject the IP addresses for a specified amount of time.
Not only do we keep multiple backups of all files and databases relating to your code and our application. We also store our application code securely in what’s called a ‘distributed version control system’. This is a tool that makes it easy for us to collaborate as a team, while storing every change we ever make to the software.
This is linked to our automatic deployment system that allows us to run automated tests on our application as it’s developed. The idea is to ensure that fewer bugs are introduced as we improve our software and extend the product to meet your business requirements. Not only does it make development easier, but it also ensures we never lose the application code. It ensures that we can deploy the application quickly in case of any emergency in the quickest amount of time possible.
CloudFlare
– https://www.cloudflare.com/features-security/
